Linux Vpn Iptables Port Forwarding Without Snat
Hey there, fellow Linux adventurer! Ever wanted to access a service running on a machine tucked away behind a VPN, but without the usual hassle of SNAT (Source Network Address Translation)? Yeah, me too! It can feel like trying to solve a Rubik's Cube blindfolded, right? But fear not! We're going to crack this nut together, and it's going to be way easier than you think. Think of it as the "ninja warrior" course of networking, but with less mud and more keyboard clicks.
Why Bother with No SNAT?
Okay, so why are we even ditching SNAT? Well, with SNAT, the original source IP gets hidden. That's great for some things, like general browsing security, but not so great when you want the destination server to know who's connecting. Maybe you have a firewall rule based on source IP, or you're running some fancy application that needs the client's real address. Imagine trying to deliver a pizza without knowing where it came from - chaos!
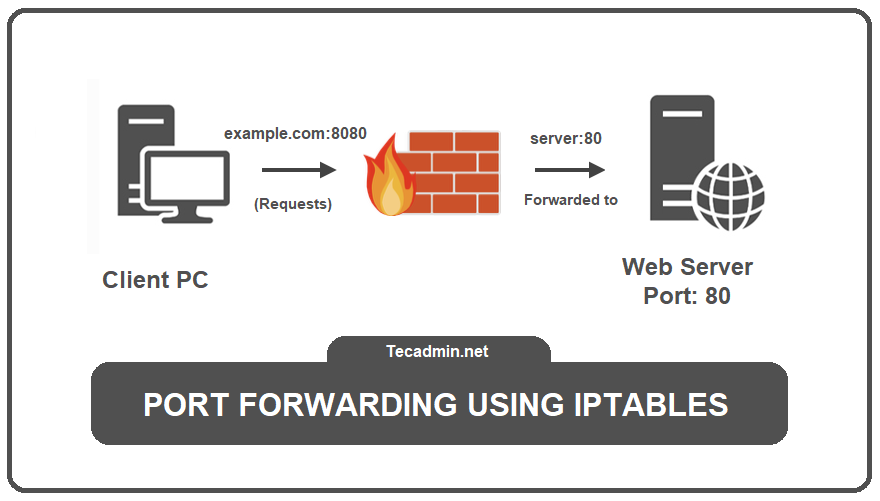
The Core Idea: Port Forwarding with iptables
The secret ingredient is iptables, the incredibly powerful (and sometimes intimidating) firewall tool in Linux. Don't worry, we'll tame it. We're basically going to tell iptables to forward traffic arriving on a specific port (the one you want to access) to the internal IP address of your VPN client.
Must Read
Let's Get Our Hands Dirty (But Not Literally)
First things first, you'll need to know a few things:
- The external IP of your VPN server. This is the address you'll be connecting to.
- The port you want to forward. Let's say it's port 8080 (because why not?).
- The internal IP address of your VPN client. This is the machine behind the VPN that you want to reach. It might be something like 10.8.0.2 (a common VPN address).
- Your network interface that faces the internet. This is usually something like eth0, wlan0 or ens3. You can figure it out using `ip addr` command.
Ready? Let's fire up the terminal! (Don't worry, it won't explode.)
The Iptables Magic
We'll use a few iptables commands. I suggest you copy and paste them to avoid typos:
First, we need to enable IP forwarding. This tells the kernel to actually forward packets between interfaces:

echo 1 > /proc/sys/net/ipv4/ip_forward
Important: This only lasts until the next reboot! To make it permanent, edit `/etc/sysctl.conf` and uncomment the line `net.ipv4.ip_forward=1`. Then, run `sysctl -p` to apply the changes.
Next, we set up the forwarding rule in the nat table, in the PREROUTING chain:
iptables -t nat -A PREROUTING -i <your_external_interface> -p tcp --dport 8080 -j DNAT --to-destination 10.8.0.2:8080
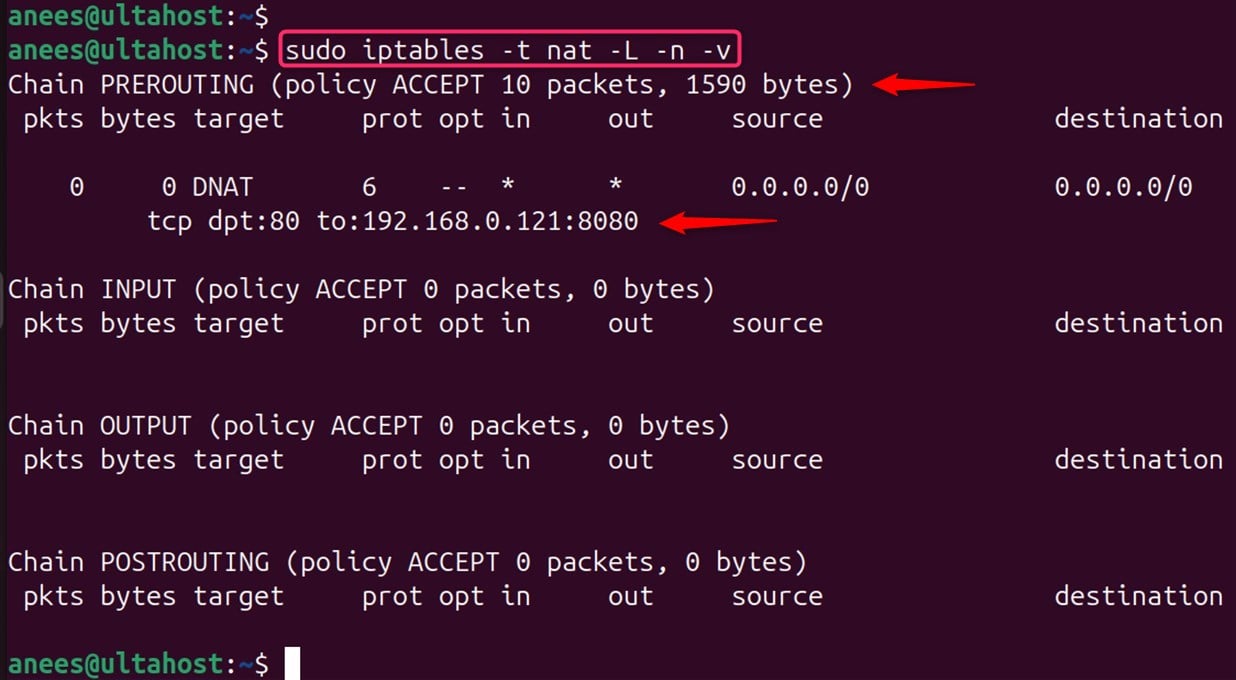
Replace <your_external_interface> with your network interface, and 10.8.0.2 with the actual internal IP of your VPN client.
This command says, "Hey iptables, if someone connects to port 8080 on my external interface, change the destination to 10.8.0.2:8080".
Finally, and this is the crucial bit for skipping SNAT, we need to allow the traffic to be forwarded on the FORWARD chain in the filter table:
iptables -A FORWARD -i <your_external_interface> -o tun0 -d 10.8.0.2 -p tcp --dport 8080 -j ACCEPT
iptables -A FORWARD -i tun0 -o <your_external_interface> -s 10.8.0.2 -p tcp --sport 8080 -j ACCEPT
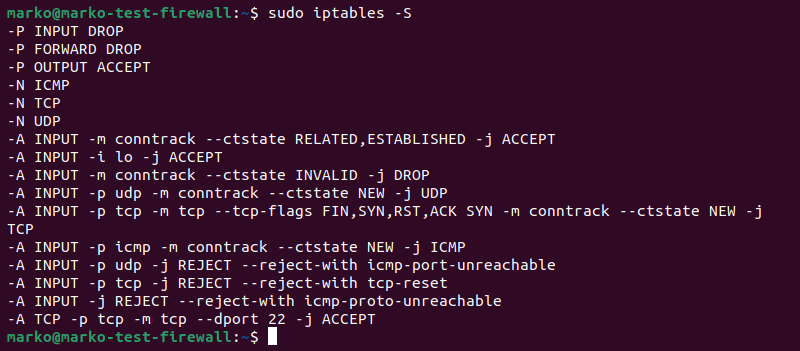
Replace tun0 by the interface assigned to your VPN if it is other one.
These commands allows incoming and outcoming traffic on the specified interface for the forwarded port.
Testing, Testing, 1, 2, 3
Now for the moment of truth! From a machine outside your VPN, try connecting to your VPN server's external IP on port 8080. If everything is set up correctly, you should be able to access the service running on your VPN client! Give yourself a pat on the back – you've earned it!
Making it Stick
Like the `ip_forward` setting, iptables rules are also cleared on reboot. You'll need to save them! The method depends on your distribution. On Debian/Ubuntu, you might use `iptables-persistent`. On CentOS/RHEL, you could use `iptables-save`. Consult your distribution's documentation.
Troubleshooting Tips
* Firewall on the VPN client: Make sure the VPN client isn't blocking the incoming connection.
If it does not work, check the VPN client default configuration. It might overwrite the FORWARD policies. If this is the case, then configure your vpn to accept custom policies in the FORWARD chain.
* Double-check your IPs and ports: Typos are the enemy of all sysadmins!
* Logging: Use iptables logging (the `-j LOG` target) to see if packets are being dropped.
Conclusion
And there you have it! You've successfully configured Linux VPN iptables port forwarding without SNAT! It might have seemed daunting at first, but with a little persistence and a sprinkle of Linux magic, you've conquered another networking challenge. Now go forth and build amazing things, knowing you have the power to bend the internet to your will! You're awesome! Keep on exploring and happy networking!
