Cisco Asa 9.6 Packet Flow

Ever feel like your internet connection is a sophisticated, digital dance party that you're only vaguely aware of? Well, you’re not entirely wrong! Deep within your network, a silent guardian – possibly a Cisco ASA firewall – is orchestrating the flow of data, making sure only the right guests (packets) get past the velvet rope.
Today, we're taking a breezy stroll through the Cisco ASA 9.6 packet flow. Think of it as understanding the bouncer at the coolest online club – knowledge that's surprisingly useful, even if you're not a network engineer.
The Packet's Journey: A VIP Tour
Imagine a tiny digital courier, a packet, arriving at your ASA's door. This isn’t just a random collection of bits; it's a meticulously organized package with a destination and instructions. The ASA 9.6 uses a specific sequence to determine what happens next.
Must Read
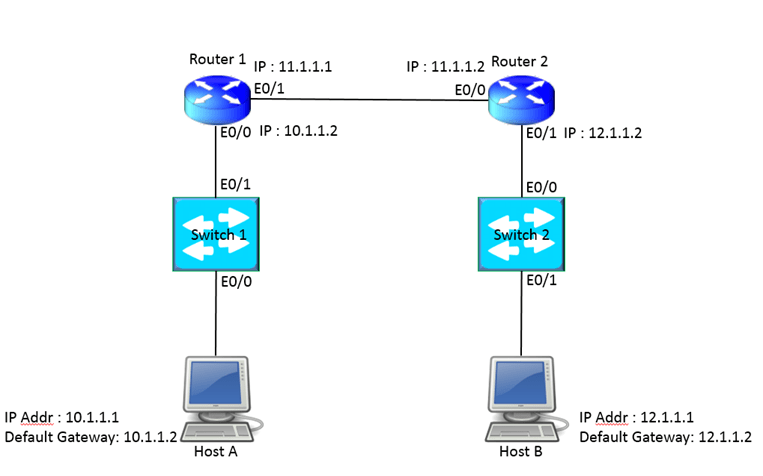
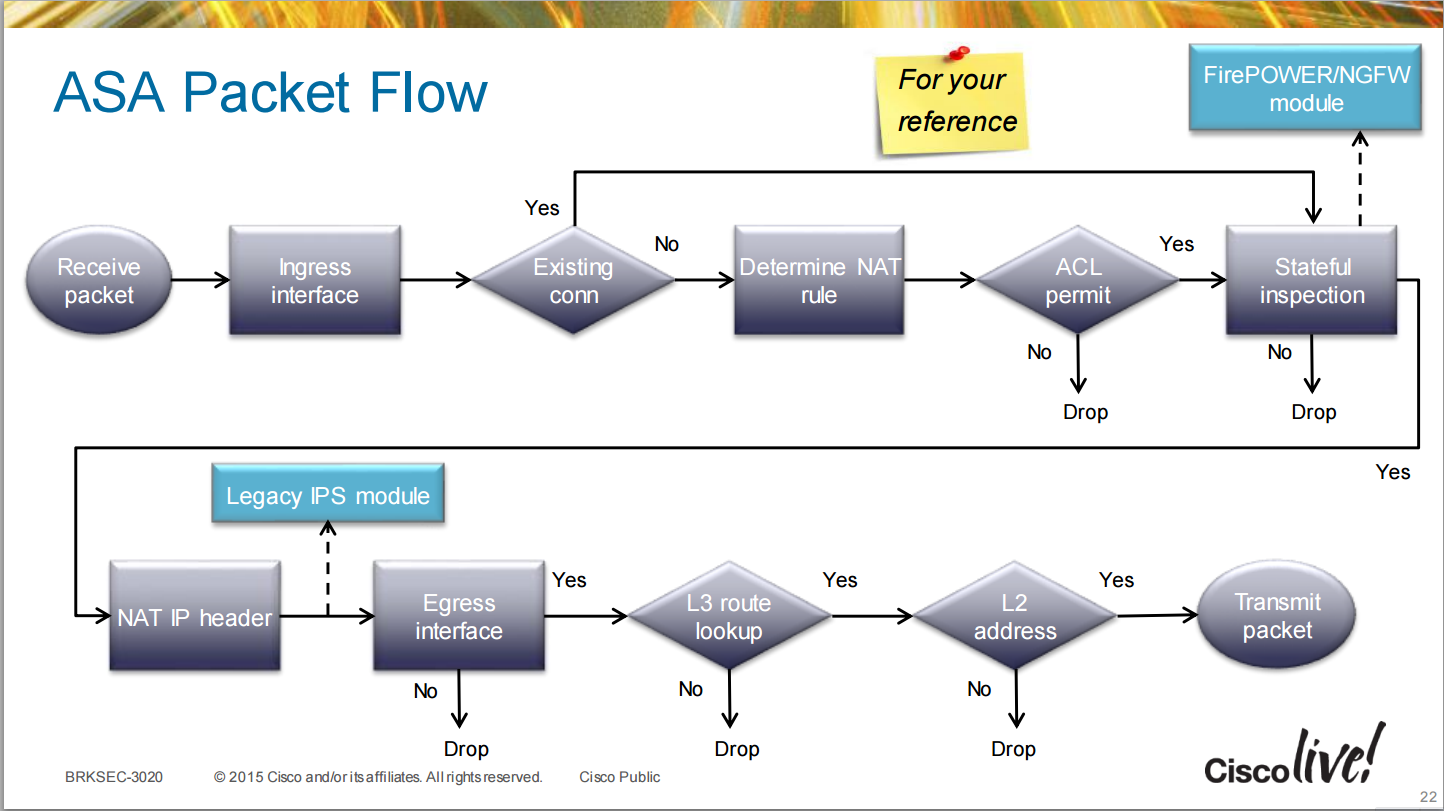
Step 1: Ingress Interface. Like arriving at the check-in desk. The ASA first looks at the ingress interface, the physical port the packet arrives on. Think of it as the bouncer scanning your ticket. The firewall needs to identify where the packet comes from before anything else. Is it from your internal network (trusted) or the internet (less trusted)?
Step 2: Access Control List (ACL) Check. This is where things get interesting. The ASA consults its Access Control Lists, essentially a list of rules that determine who gets in. Picture it as a velvet rope, and the ACLs are the criteria for getting past. Is this packet from a known IP address? Is it trying to access a forbidden service? If it violates the rules, poof, denied!
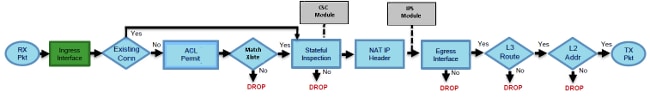
Step 3: NAT (Network Address Translation). NAT is like giving your packet a disguise. If your internal network uses private IP addresses, NAT translates them to a public IP address before the packet heads out to the internet. It's like a secret handshake for communicating online, hiding your internal structure from prying eyes.
Step 4: Route Lookup. Where does this packet need to go next? The ASA consults its routing table, a map that shows the best path to the destination. It's akin to a GPS guiding your packet on its journey.

Step 5: VPN (Virtual Private Network) Check. If the packet is part of a VPN connection, the ASA handles encryption and decryption, ensuring secure communication. Think of it as a private tunnel for your data to travel safely.
Step 6: Egress Interface. Finally, the packet is ready to be sent on its way. The ASA selects the egress interface, the physical port the packet exits from, and sends it onward. This is the digital equivalent of pushing the packet out the door and saying, "Good luck!"
Fun Facts and Tips for the Savvy User
- Did you know the concept of packet switching dates back to the 1960s? It’s a testament to how long some fundamental technologies have been around.
- Security Zones are your friends! Organize your interfaces into zones (e.g., inside, outside, DMZ) to make your ACLs more manageable.
- Regularly review your ACLs. Stale rules can create security vulnerabilities or hinder network performance.
- Think of NAT like a one-way mirror. Internal clients can initiate connections to the outside world, but external clients typically can't initiate connections directly to internal clients unless specifically configured.
Beyond the Firewall: Echoes in Everyday Life
Understanding packet flow might seem like a deeply technical exercise, but it has echoes in our daily lives. Just like the ASA carefully controls the flow of data, we constantly manage the flow of information in our own lives. We filter news feeds, prioritize tasks, and choose who to grant access to our personal space. The principles of filtering, routing, and security apply to both networks and personal well-being.
Next time your internet is running smoothly, take a moment to appreciate the unsung hero that is your firewall. It's working tirelessly behind the scenes, ensuring your digital dance party keeps rocking!